SSL Server Test, going from rating C to A
This week I was listening to the More Than Just Code podcast #85 and one the picks this time was Qualys-SSL Labs for their SSL Server Test. This prompted me to test my own web server www.littlegemsoftware.com. The test gave me a disappointing C-rating with several issues
- This server is vulnerable to the POODLE attack. If possible, disable SSL 3 to mitigate. Grade capped to C.
- This server accepts RC4 cipher, but only with older protocol versions. Grade capped to B.
- The server does not support Forward Secrecy with the reference browsers.
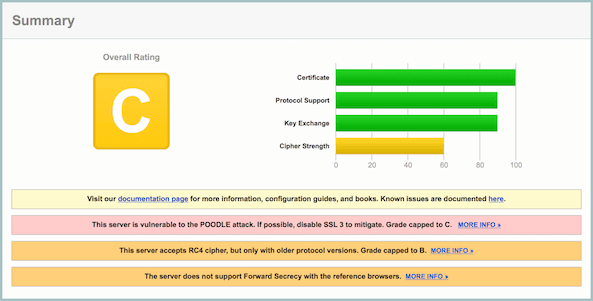 Rating C
Rating C
Resolving the vulnerability to POODLE attack
Based on the article ‘How To Protect your Server Against the POODLE SSLv3 Vulnerability’ I made a change to ssl.conf to disable both SSLv2 and SSLv3. Within the default version of ssl.conf all SSL protocol were enabled
SSLProtocol allby changing this line into the following both SSLv2 and SSLv3 are being disabled
SSLProtocol all -SSLv2 -SSLv3Retesting my web server with this change in place gave a B-rating.
Supporting Forward Secrecy
Made another change to ssl.conf by adding the following lines (based on information taken from ‘Configuring Apache, Nginx, and OpenSSL for Forward Secrecy’)
SSLHonorCipherOrder on
SSLCipherSuite "EECDH+ECDSA+AESGCM EECDH+aRSA+AESGCM EECDH+ECDSA+SHA384 EECDH+ECDSA+SHA256 EECDH+aRSA+SHA384 EECDH+aRSA+SHA256 EECDH+aRSA+RC4 EECDH EDH+aRSA RC4 !aNULL !eNULL !LOW !3DES !MD5 !EXP !PSK !SRP !DSS"Retest still gave me the B-rating but the notice about not supporting forward secrecy was gone.
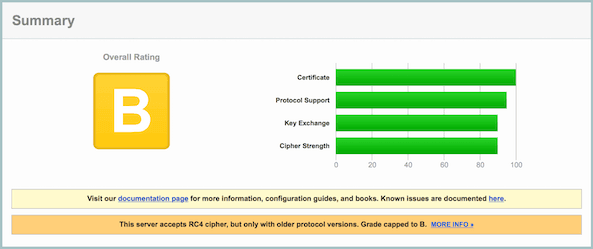 Rating B
Rating B
Stop accepting RC4 ciphers
By changing the SSLCipherSuite to the following, disabling the use of RC4 completely, finally gave me the A-rating.
SSLCipherSuite "EECDH+ECDSA+AESGCM EECDH+aRSA+AESGCM EECDH+ECDSA+SHA384 EECDH+ECDSA+SHA256 EECDH+aRSA+SHA384 EECDH+aRSA+SHA256 EECDH+aRSA+RC4 EECDH EDH+aRSA RC4 !aNULL !eNULL !LOW !3DES !MD5 !EXP !PSK !SRP !DSS !RC4"The SSLCipherSuite is the same one as used before, but has !RC4 to the end
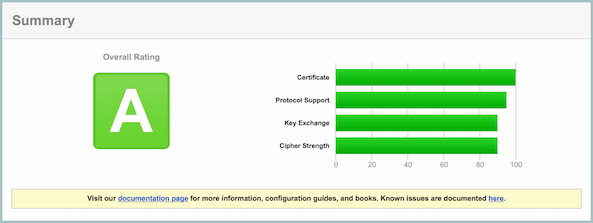 Rating A
Rating A